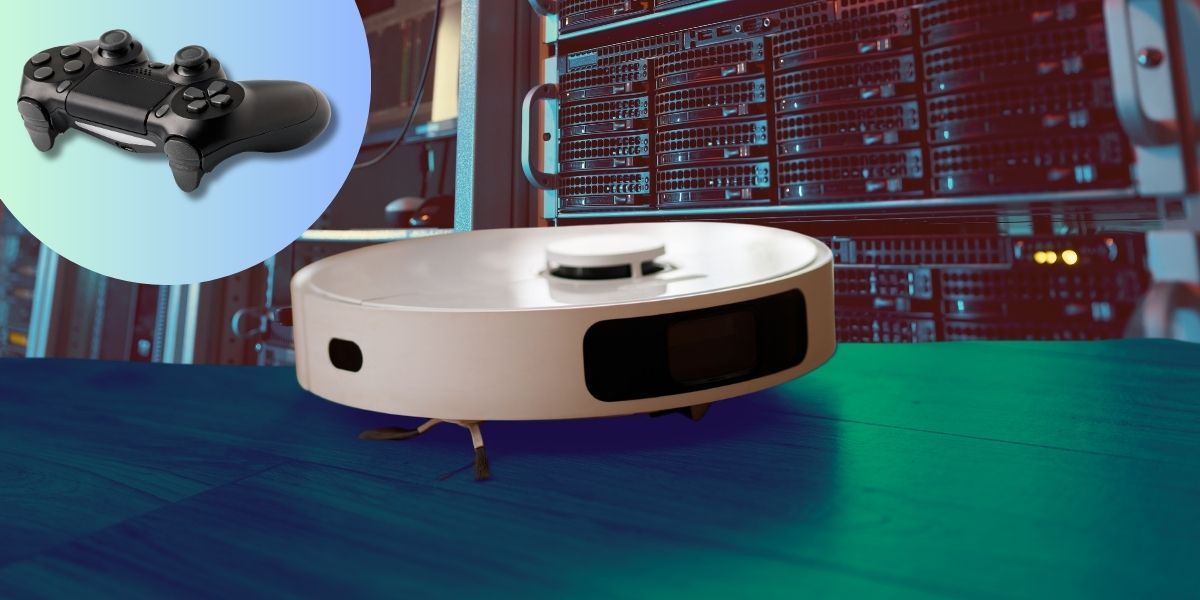
Most people are happy enough letting their robot vacuum do its thing. Sammy Azdoufal wanted to go one step further and steer his around with a video game controller. What started as a fun weekend project quickly turned into one of the more alarming smart home security stories in recent memory.
While building a custom remote-control app for his DJI Romo, a high-end robot vacuum that retails for around $2,000, Azdoufal used an AI coding assistant to help him figure out how the device communicated with DJI’s cloud servers. To make his controller work, he needed to pull a security token that verified he was the device’s owner. Simple enough in theory. In practice, the server didn’t just hand over his credentials. It handed over access to nearly 7,000 other DJI Romo vacuums operating in homes across 24 countries, including their live camera feeds, microphone audio, floor plan maps, and approximate locations drawn from IP addresses.
To be clear, Azdoufal didn’t go looking for any of this. He reported his findings to tech publication The Verge, which then flagged the issue directly to DJI. The company says it identified the vulnerability through its own internal review in late January and pushed two patches in early February, with the fix deployed automatically so users didn’t need to do anything. No word yet on whether any third parties had independently found and exploited the same flaw before it was closed.
The DJI Romo isn’t your average budget floor-sweeper. It’s a premium, camera-equipped device roughly the size of a large terrier when parked at its dock, and it’s currently rolling out across international markets after launching in China last year. Like most modern robot vacuums, it builds detailed maps of your home to navigate efficiently, and some of that data is stored remotely on manufacturer servers rather than on the device itself. That remote storage is what made the vulnerability possible.
The incident lands in the middle of a broader moment of reckoning around smart home privacy. Earlier this month, Amazon’s Ring division sparked backlash after a Super Bowl advertisement for its pet-tracking feature was widely read as a pitch for neighbourhood-wide surveillance. Around the same time, Google confirmed it was able to retrieve footage from a Nest Doorbell camera for an abduction investigation, even though the owner had believed it was deleted. People are increasingly uneasy about just how much of their private lives their internet-connected devices are quietly recording and storing.
The timing is also notable given ongoing scrutiny of Chinese technology companies operating in Western markets. DJI, best known for its drones, has faced years of political pressure in the United States over data security concerns, with some of its products already banned from government use. Those concerns are still contested and evolving, but incidents like this one do little to ease them.
What makes Azdoufal’s story particularly pointed for the tech industry is the role AI played in it. He used an AI coding assistant to do the reverse engineering, which means the technical barrier to uncovering this kind of flaw has dropped considerably. Security researchers have long warned that smart home devices are attractive targets precisely because they live in our most private spaces. As robot vacuums, smart doorbells, and even humanoid home robots become more common, the potential consequences of a security lapse grow far more serious. All Azdoufal wanted was a fun weekend project. The rest of us are left wondering what else might be listening.